Many of you who have followed my personal blog and/or posts on VMware Network Virtualization blog, know I have focused on and presented on NSX Multi-site Solutions and Disaster Recovery the last few years at VMworld. This year, I transitioned to focus specifically on VMware Cloud on AWS. Below I give a brief overview of some of the details I covered in the session. You can now see the recorded session for free here. I will also be repeating this session at VMworld in Barcelona in November.
I always enjoy attending VMworld to present and meet with customers. This year, I had the added bonus of doing a book signing for my new VMware Press Book: VMware NSX Multi-site Solutions and Cross-vCenter NSX Design; you can download the free PDF/eBook here.
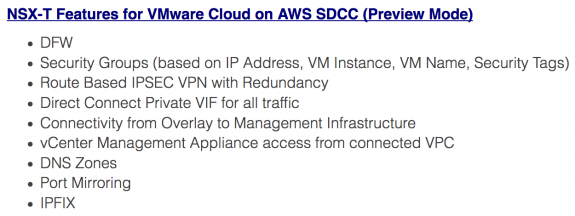
Also, I was excited this year to present on the latest and greatest with NSX networking and security in VMware Cloud on AWS. In my session, VMware Cloud on AWS with NSX – Use Cases, Design, and Implementation, I utilized the majority of the the time to discuss the advanced networking and security capabilities coming to VMware Cloud on AWS with the underlying networking and security platform changing from NSX-V to NSX-T; currently in preview mode.
See my prior post on VMware Network Virtualization Blog: VMware Cloud on AWS: Advanced Networking and Security with NSX-T SDDC where I discuss a lot of these new advanced networking and security capabilities.
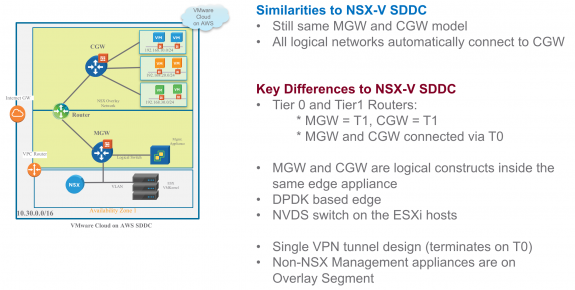
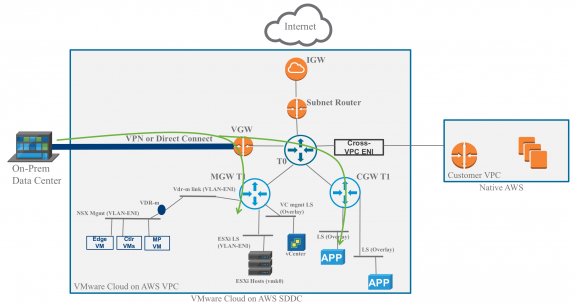
In the VMworld session, before digging into the above features, I also provide some details on underlying architecture changes and respective benefits.
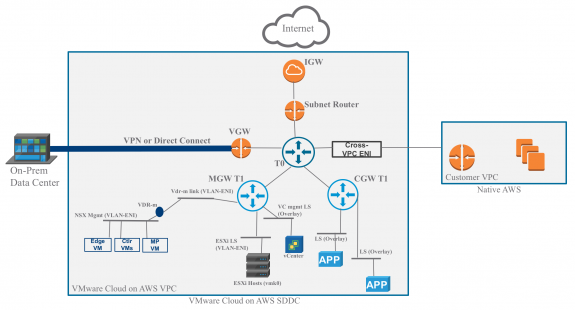
Below are some details on changes in underlying architecture and benefits from the NSX-T design.
1. vCenter management network is an overlay: can leverage same operational/troubleshooting tools as for compute workloads
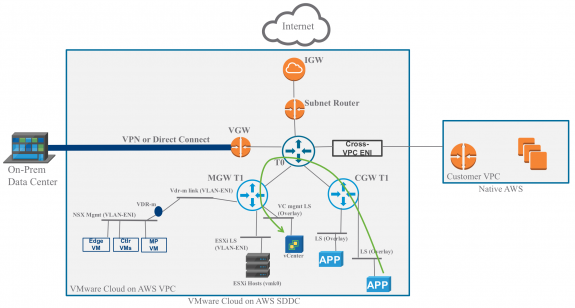
2. Workloads behind CGW can talk to management components behind MGW via T0 router; workloads on network segments can can run management tools and automation scripts calling vCenter and NSX Policy Appliance private endpoint APIs
3. ESXi host access from overlay; leveraged by new port mirroring and IPFIX capabilities. You can now run tools like Wireshark and Plixer Scrutinizer on workloads behind CGW and leverage port mirroring and IPFIX capabilities that need access to the ESXi hosts
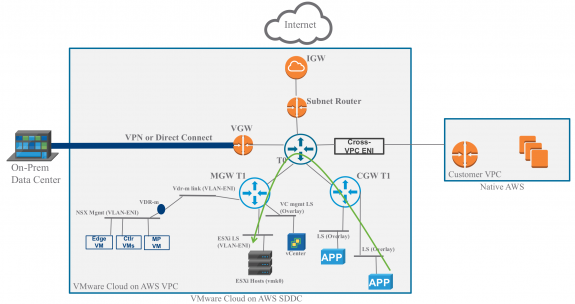
4. vCenter management network accessible from native AWS customer VPC; can leverage automation tools running on EC2 instances which can access the vCenter management network
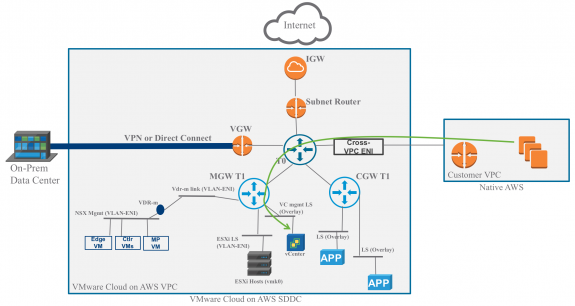
5. All traffic (ESXi hosts, management appliance, workload, vMotion, and cold migration traffic) is supported over Direct Connect Private VIF simplifying Direct Connect connectivity from on-prem to VMware Cloud on AWS SDDC
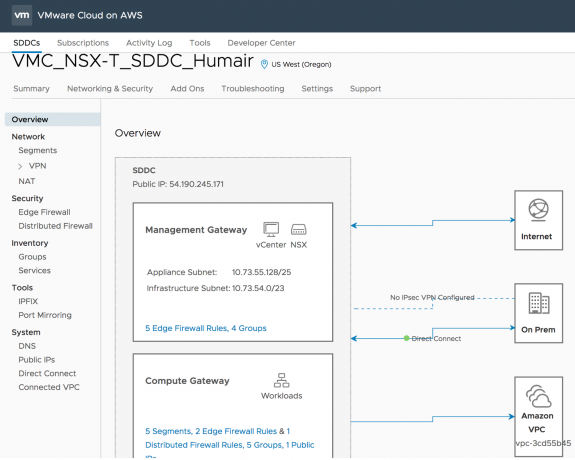
I also discuss the new layout for the Networking & Security tab and how it has been enhanced to provide ease of usability; the menu on the left can be used to easily identify and move between different configurations.
Finally, I wrap-up with some design considerations for connectivity to on-prem with Direct Connect and IPSEC Route Based VPN, and L2VPN.
With NSX-T SDDC comes the enhancement where all traffic is now supported over Direct Connect Private VIF. This greatly simplifies connectivity and configuration, and VPNs are no longer required to carry certain traffic. Prior, only ESXi managemnet, vMotion, and cold migration traffic were supported over Direct Connect and IPSEC VPNs had to be established either over Internet or Direct Connect public VIF to carry all other traffic; needless to say, there was more complexity involved here then desired. See my prior blog post on this on the VMware Network Virtualization Blog here.
Now Direct Connect private VIF can be utilized to carry all traffic between on-Prem and VMware Cloud on AWS SDDC, simplifying the solution. Once, Direct Connect is established, the entire VPC CIDR, Mgmt Appliance Network, and NSX Network Segments are automatically advertised to on-prem via BGP. Below is an illustrated example; users’s can setup multiple Direct Connect private VIFs for redundancy.



 Twitter
Twitter LinkedIn
LinkedIn Youtube
Youtube RSS
RSS
1 Response to VMworld 2018: VMware Cloud on AWS with NSX – Use Cases, Design, and Implementation