Cloudflare Bot Management can better detect and help mitigate malicious bots using multiple detection mechanisms like heuristics, behavioral analysis/anomaly detection, machine learning, and finger printing against a massive global volume of data. My colleague and I recently discussed and showed examples of some of these capabilities in a recent Cloudflare webinar.
In the demo I walked through our heuristic, behavioral analysis/anomaly detection, and machine learning engines showing how the heuristics engine is able is able to leverage attributes of the request to identify if the request is automated (Ex: specific well known user agents and other request attributes).
If the heuristics engine identifies the request as being definitely automated, it gives it a bot score of 1. Bots score of 1 mean automated traffic and bot scores of 2 – 29 means likely automated; if interested, you can read more about bot scores here.
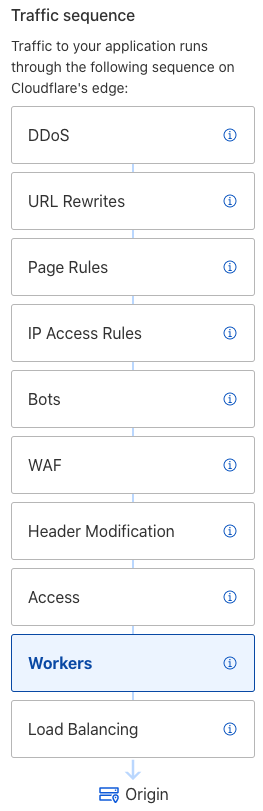
Leveraging Cloudflare bot scores, customers can block, allow, challenge, log, and do all sorts of interesting things like even manipulate the request using serverless code via Cloudflare Workers.
From the traffic sequence on the left, you can see Cloudflare Bot Management is run prior to Cloudflare WAF and Workers, allowing these tools to leverage the bot score. For example, is a competitor trying to undercut your pricing by price scraping? Based on bot score for that specific request, you can use Workers to modify the response and send them back false prices/data!
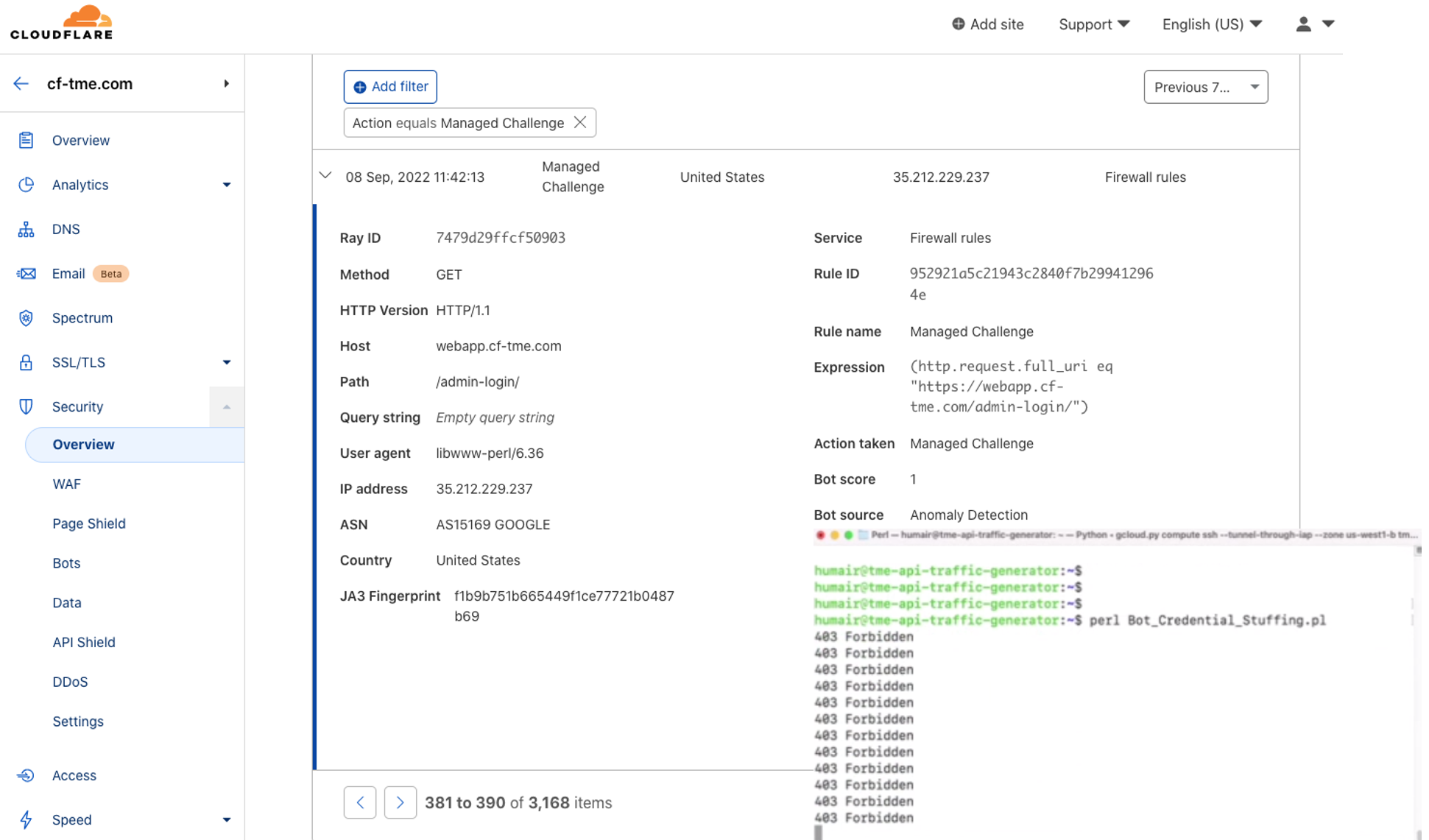
In the demo I also used a bot I wrote in Perl to show how Cloudflare bot management can easily stop credential stuffing attacks. A credential stuffing attack is when a hacker tries to gain access to or take over an account usually by obtaining a list of stolen credentials. The hacker will write or utilize an existing tool to loop through the stolen credentials and try applying them one-by one to a specific login page of an application/site they’re trying to gain access to.
In the webinar demo, the bot first tries to get information from the page, including the specific forms/fields from a login page and then tries to loop through a list of credentials and populate and respectively submit the form in an attempt to login.
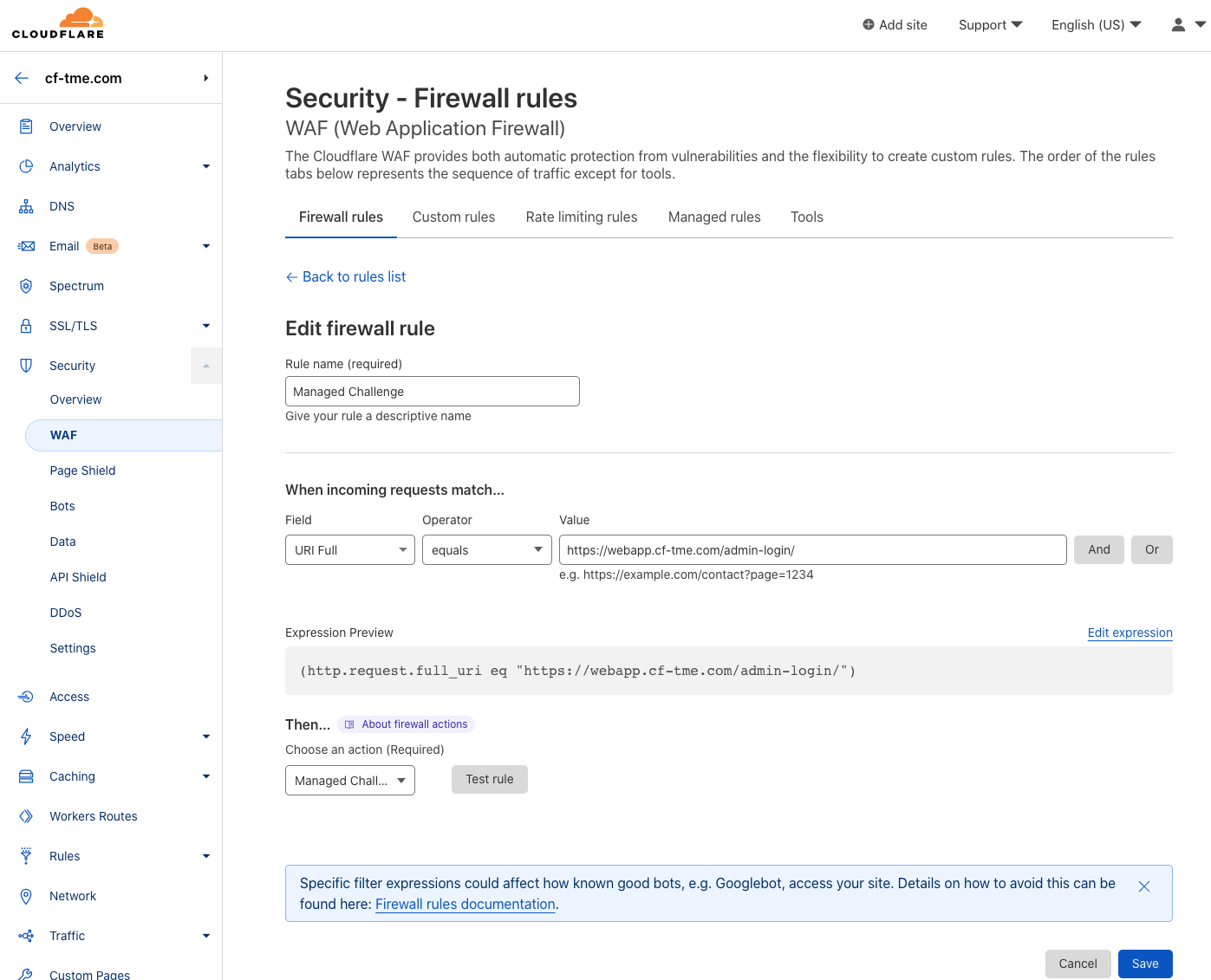
I demoed Cloudflare Managed Challenge which also leverages Cloudflare’s bot detection engines and respective learned information from the request. With Managed Challenge Cloudflare dynamically chooses the appropriate type of challenge based on the characteristics of the request. The goal is to minimize any type of interaction/CAPTCHAs. In most cases, a non-interactive challenge will be performed.
In this case I created a WAF rule where Managed Challenge is used for a specific login page as shown below.
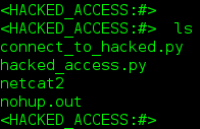
I demonstrated being able to successfully access the login page as a human via a browser. Then I contrasted that with trying to access the page for malicious purposes as a bot. From the below screen shots, you can see when I ran the malicious bot to try to hack the login, Managed Challenge was the action taken. The bot score was 1 and anomaly detection picked-up the request as out of the ordinary when compared to a continuously updated baseline based on requests to this login page. You can see the bot is stopped cold in its tracks.
Now, I wanted to demonstrate a few things with Managed Challenge in this case. Typically, a customer would just create a WAF rule to block on a bot score of 1 which is identified by Cloudflare as automated traffic.
Click the webinar link below to see the webinar recording showing the demo described in this blog and learn more about Cloudflare Bot Management.
My blogs on HumairAhmed.com
Follow me on Twitter.



 Twitter
Twitter LinkedIn
LinkedIn Youtube
Youtube RSS
RSS