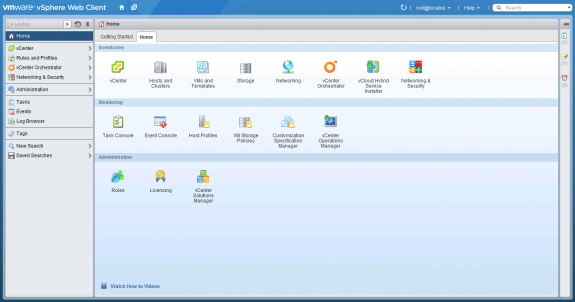
If you haven’t already, please checkout the Dell-VMware NSX Reference Architecture (RA) whitepaper. In the reference architecture I explain in detail the foundational NSX-vSphere components and also how Dell can provide a complete end-to-end infrastructure (servers, networking, storage) to support a robust SDN solution with NSX. In this blog, I will provide a quick overview, some insight on NSX, and examples of VMware NSX deployment with a complete end-to-end Dell infrastructure.
This detailed RA covers the specifics on a complete end-to-end VMware NSX-vSphere design/deployment also taking into account all physical infrastructure components such as NICs/CNAs, servers, underlay network switches, and storage. I have yet to see a complete end-to-end detailed RA from another hardware networking vendor. Although NSX is agnostic to the underlying hardware utilized, it is important to consider the complete end-to-end infrastructure that will be utilized in a NSX or any SDN environment.
Obviously, your logical networks ride on the physical network or the piping underneath. Although it is true that the network services are being decoupled from the underlying hardware and the only true requirement from the underlay network is IP connectivity, it is also true that since your logical networks ride on the physical network, you need to ensure you have a robust physical underlay network. The nice thing VMware NSX brings to the table in this respect is it normalizes the underlying network and removes complex requirements that different vendors may enforce with proprietary features. NSX simply requires IP connectivity for the underlay and a slightly larger MTU on the physical network (1600 bytes) to account for the VXLAN/encapsulation header.
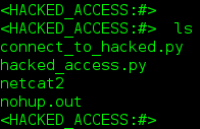
Along with your physical underlay network, you should ensure your server and storage connectivity are good. In the Dell-VMware NSX Reference Architecture whitepaper a hybrid rack and blade server solution is used.
Below is a design of a Dell-VMware NSX solution leveraging a complete Dell hardware infrastructure; it leverages a converged network with DCB and iSCSI. All blade/rack servers have only 2 x 10 GbE CNAs and carry all LAN/SAN traffic.
Spending extensive amounts of time studying, working in the lab, and writing RAs/designs for NSX, I’ve come to appreciate the benefits and possibilities with NSX as an SDN solution first-hand. It’s not just that any SDN solution can provide flexibility and similar benefits, it’s that VMware makes it easy and logical as they did with server virtualization. This is one of their strengths, and being the dominant leader in server virtualization, they’re in great positioning to capitalize on SDN with NSX, and Dell is a vendor in great positioning to deliver all the hardware infrastructure.
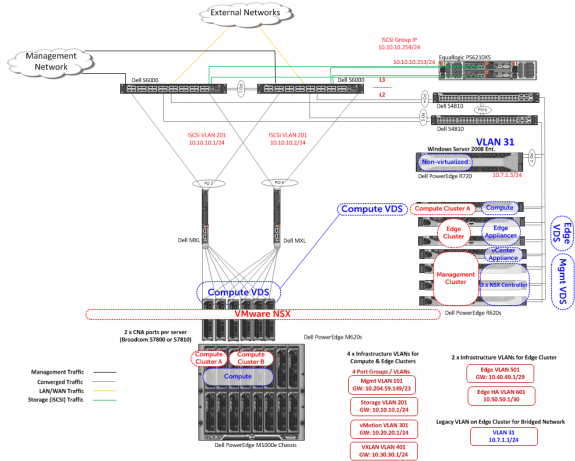
Below is a logical design of the same setup.
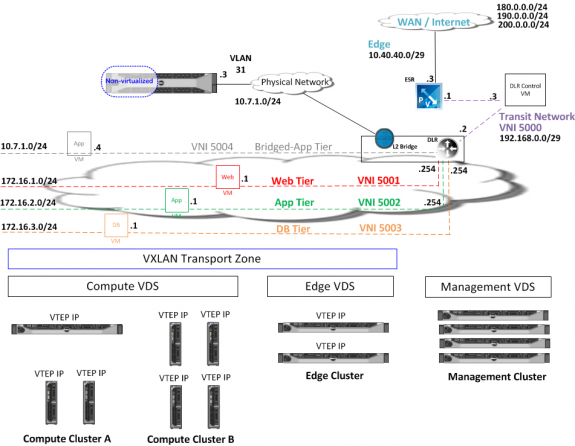
Once the NSX plugin is installed in vCenter via NSX Manager virtual appliance, you will see the new “Networking & Security” menu item on the left-hand side as shown below.
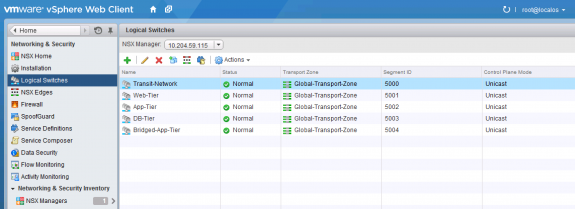
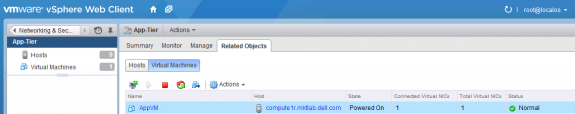
Once all the physical and virtual infrastructure is setup and configured, you can start creating logical networks in minutes and start moving and creating VMs into the respective logical switches/networks. The flexibility, automation, and new architectures/designs (especially for security) this enables brings tremendous value. In the below two figures, I show the logical switches/networks in my diagram and show a VM that has been moved from a traditional VLAN to the ‘App-Tier’ logical switch; the VM is now no longer tied to the underlying physical network hardware.
The below shows my NSX Edge appliances: the 1.) NSX Perimeter Edge (NSX Services Gateway) and the 2.) Distributed Logical Router Control VM. The NSX Perimeter Edge allows for logical networks to connect and peer with external networks while also providing network services such as DHCP, NAT, VPN, firewall, dynamic routing, and load balancing. The DLR Control VM is used to manage the Distributed Logical Router and can also be used to configure a logical bridge for bridging between logical (VXLAN) and physical (VLAN) networks.
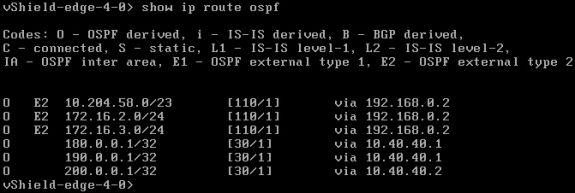
Something network engineers will find appealing is the CLI access and configuration abilities of the virtual routers. In my logical design diagram further above, I showed how the NSX Perimeter Edge router was peering with the external networks. Below I confirm via NSX Perimeter Edge CLI that the 180.0.0.0/24, 190.0.0.0/24, and 200.0.0.0/24 external networks are learned by the logical router. As you can see, VMware has done a good job to keep the syntax similar to that used by most hardware switch/router vendors.
Follow me on Twitter: @Humair_Ahmed



 Twitter
Twitter LinkedIn
LinkedIn Youtube
Youtube RSS
RSS
1 Response to Creating Logical Networks and Services with VMware NSX on Dell Infrastructure