
Ahead of this year’s VMworld which was just this past week (08/30 – 09/03), VMware recently released NSX 6.2 with many new and exciting features. You can see a list of new features listed in the NSX 6.2 online release notes. In this short post, I’ll briefly discuss the new Cross-vCenter Networking and Security (Cross-VC NSX) functionality. For more details and information, checkout the VMware NSX 6.2 for vSphere Documentation Center.
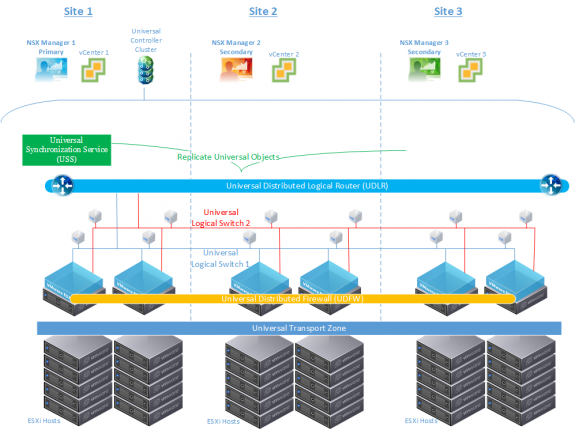
With Cross-VC NSX, introduced in NSX 6.2, logical switches (LS), distributed logical routers (DLR) and distributed firewall (DFW) can now be deployed across multiple vCenters. These Cross-VC NSX objects are called Universal objects. The universal objects are similar to distributed logical switches, routers, and firewall that we’re already familiar with, except they have global or universal scope, meaning they can span multiple vCenter instances. So, now, in addition to the prior local-site scope objects, users can implement Universal Logical Switches, Universal Logical Routers, and Universal DFW across a multi-vCenter environment that can be within a single data center site or across multiple data center sites.
Let’s clarify a few things about Cross-VC NSX:
– there is still a 1:1 relationship with NSX Manager and vCenter.
– one NSX Manager will have a primary role and the rest will have secondary roles. After assigning the primary role to the first NSX Manager, additional NSX Managers can be registered as secondary.
– up to eight NSX Managers/vCenters are supported, with one NSX Manager being primary.
– the primary NSX Manager will use the Universal Synchronization Service (USS) to replicate only the Universal objects to the secondary NSX Managers.
– 1 Universal Transport Zone is supported and all Universal objects will be part of this Universal Transport Zone spanning across multiple vCenter environments.
– All Universal objects must be created/managed via the primary NSX Manager.
– 3 NSX controllers are supported and the same three NSX controllers are used by all NSX Managers/sites. This Universal Controller Cluster is associated with the primary NSX Manager. As secondary NSX Managers are registered, the respective controller information is imported to the secondary NSX Managers, and the controllers are shared with all NSX Managers.
An example logical design is shown below:
Some of the benefits of such a design are immediately clear. First, we are now able to enable logical networking and security for application workloads that span multiple vCenters or multiple physical locations. For instance, VMs can now vMotion across vCenter boundaries with consistent security policy enforcement and without having to manualy modify/provision networking and security services. In effect, NSX control and automation is being expanded across vCenter boundaries whether within or across data centers.
VMs that have policies defined under the Universal rule section can be moved across hosts that belong to different vCenters. Further, Security Groups based on IP Address, IP Set, MAC Address and MAC Set can be used in Universal rules, and the respective Security Groups and group memberships are synced across secondary NSX managers by the VSS on the primary NSX Manager; this helps ensure security policy consistency in Cross-VC NSX environments.
Firewall policies can still be applied only to the local vCenter/NSX environment if desired, but any rules applied under the Universal section will be applied to the universal scope and override the local rules.
Another cool feature is local egress on the UDLR. If local egress is enabled when a UDLR is created, a unique ID called the locale ID is associated to the routes in a specific location. Routes are sent by the universal controller cluster to hosts only when the host locale ID matches the locale ID associated with the route. You can also selectively send routes to hosts by configuring the locale ID on specific hosts or on a cluster of hosts.
Local egress allows north-south traffic to be efficiently routed out the local site uplink; this enables localized north-south routing based on the physical location of the workloads and improves upon multi-site deployment scenarios. I’ll discuss this feature in more detail in a later blog on multi-site deployments.
To learn more about Cross-VC NSX and additional new features like operations and trouble shooting features/enhancements: Central CLI, trace flow, CLI monitoring, communication channel health monitoring, etc.; logical networking and routing enhancements; edge service enhancements; security enhancements like DHCP snooping and ARP snooping; and solution interoperability enhancements see the VMware NSX 6.2 for vSphere Documentation Center.
Follow me on Twitter: @Humair_Ahmed


 Twitter
Twitter LinkedIn
LinkedIn Youtube
Youtube RSS
RSS
Hi!
Thanks for the nice article.
Indeed, a cool feature that VMware added is Local Egress. The only thing is: How do you route ingress traffic from physical world and avoid tromboning and asymmetric routing ?