Access lists (ACLs) are basically statements that packets are compared against for the purpose of taking some action if a match occurs. After an access list is created, it can be applied to inbound or outbound traffic; in some cases it is applied in both directions. You can think of an ACL as a method for filtering packets that meet a specific criteria so further action can be taken on them.
There are two types of access lists that can be created: standard and extended. In this blog I discuss only standard access lists as I will write about extended access lists in another blog.
There are a few things to keep in mind when creating access lists:
– Packets are always compared sequentially against each line of an access list.
– Once a match is found against any line in the access list, the corresponding action is taken and no more comparisons are made.
– There is an implicit “deny” at the end of every access list; this means if a packet reaches the end of an access list without any matches, the packet will be discarded. So if an access list does not have at least one permit statement, it will deny all traffic.
– Access lists will filter traffic going through the router but will not filter traffic originating from the router.
– You can only assign one access list per interface per protocol per direction.
– You cannot remove one line from an access list. Any new entries will be added to the bottom of the list. To edit a list you will have remove the list completely and recreate it. You can get around this issue by using named access lists which are simply a specific type of standard or extended access list.
With standard access lists it is important to know that the only criteria you can compare against is the source IP address in the IP packet. This means all decisions are made in regards to the source IP address of the packet. Extended access lists, which I will discuss in another blog, greatly expand the criteria that can be compared against.
As standard access lists can only match against the source IP address of the packet, they are always placed as close to the destination as possible. In consequence, the packet traverses the entire network before it is denied. This is the reason why extended access lists are more often used as they are placed as close to the source as possible saving on bandwidth.
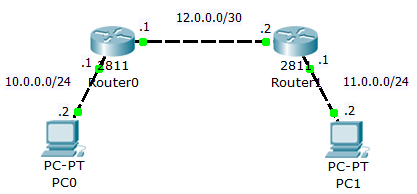
Below is my network setup for this lab. I use two Cisco 2811 [IOS 12.4(15)T1] routers. I have already setup the network and configured OSPF. If you need a brush-up on OSPF, see my prior lab, Setup OSPF on Force10 Switches or OSPF Explained and Useful Troubleshooting Commands.
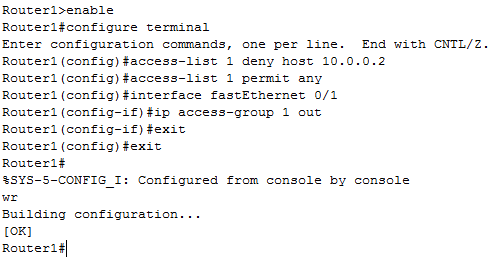
Below are the commands used on “Router1” to prevent all traffic from host 10.0.0.2 going out interface fastEthernet 0/1 of “Router1”.


 Twitter
Twitter LinkedIn
LinkedIn Youtube
Youtube RSS
RSS
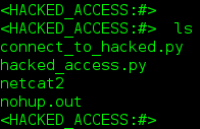
These people have been doing this for more than 12 Mos. They’re denying my comm. Services. Additionally om at a motel. WTF are they doing here. OVERWELMED!